Key takeaways:
- In 2026, a ransomware attack often targets backups and recovery systems, not just production data.
- A stronger disaster recovery plan needs immutable backups, object locking, isolation, and clean recovery workflows.
- Cloud-based disaster recovery and DRaaS only work when they shorten real downtime and support controlled failback.
- Recovery now depends on reachability, validation, and continuity, not just whether a backup copy exists.
In 2026, ransomware is no longer only a data-loss problem. It’s a recovery problem. Attackers are increasingly targeting backup repositories and the systems around them, so many organizations can’t assume their fallback options will still be there when they need them most. Research shows that 89% of organizations had backup repositories targeted by attackers, while Canada’s Cyber Centre warns that many ransomware variants are built to find and delete connected backups.
That changes the standard for disaster recovery. A modern disaster recovery plan needs more than routine backup copies. It needs isolated recovery paths, immutable backups, verified restore points, and a failback process that can bring critical systems back in hours instead of slipping into days or weeks.
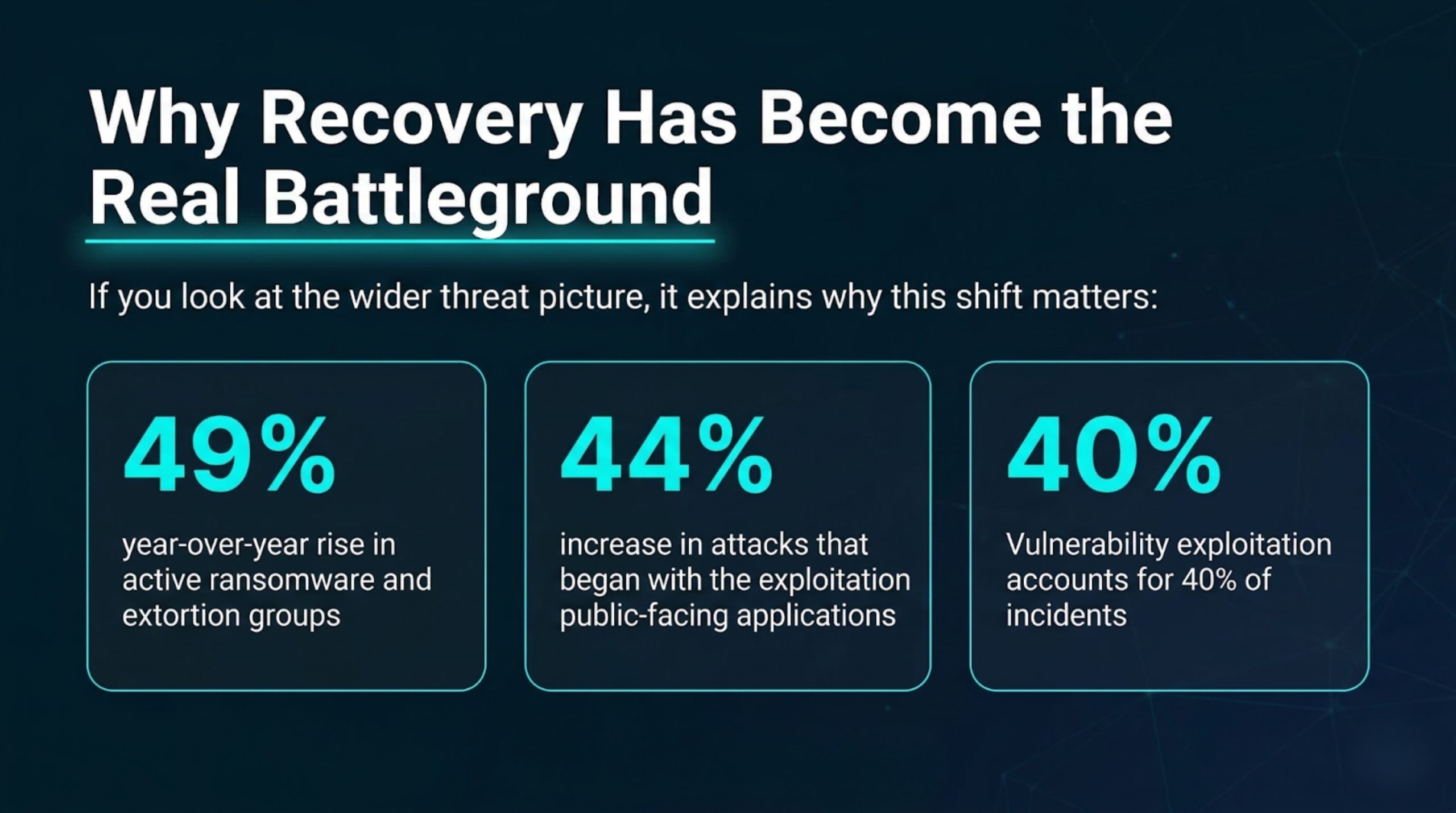
Why Recovery Has Become the Real Battleground
If you look at the wider threat picture, it explains why this shift matters:
- 49% year-over-year rise in active ransomware and extortion groups.
- 44% increase in attacks that began with the exploitation of public-facing applications.
- Vulnerability exploitation accountS for 40% of incidents.
Attackers are accelerating known playbooks with AI, leaked tooling, and repeatable methods, lowering the barrier to entry for smaller operators.
That has direct consequences for disaster recovery. Attackers don’t need to invent a brand-new method to create severe damage. They only need one open path into the environment, enough privileges to move laterally, and enough time to touch the systems that control backups, replication, and recovery. For this, threat actors actively monitor communications and plan recovery actions to undermine response efforts and push deeper into connected systems. Simply put, they aren’t only trying to lock production. They’re trying to shape what happens after the initial hit.
That’s why older assumptions break down. A disaster recovery plan built around “we’ll restore the latest backup if something goes wrong” assumes three things at once:
- It assumes the backup still exists.
- That the attacker hasn’t touched it.
- That the team can restore it without bringing the same problem back into production.
Those are dangerous assumptions in a current ransomware event. Veeam found that while 98% of organizations had some kind of ransomware playbook, fewer than half had verified backup procedures or ensured the cleanliness of their backups. Organizations that could verify integrity before recovery saw fewer reinfections and faster returns to normal operations.
Why Traditional Backup-Centered DR Falls Short
A lot of legacy disaster recovery thinking still treats backup as the finish line. If the copy exists, recovery should follow. In real incidents, that’s often where the hard part starts:
- Backup copies can be reachable from the same administrative boundary as production.
- Replication can copy corruption as quickly as it copies valid data.
- Snapshots can disappear if an attacker gains enough control.
Even when backup data survives, teams can still lose time figuring out which restore point is clean, how to stand services up in isolation, and how to reconnect users without rushing compromised systems back online.
Recovery usually breaks when teams can’t verify clean restores, can’t keep services reachable during failover, or can’t recover outside a single cloud tenant. The question isn’t only whether data survived. The question is whether the organization has a workable, controlled path back to operations.
This is also where disaster recovery ties into networking, identity, and application behavior. A VM that boots is helpful. A business service that users can actually reach is what counts. Stage2Data’s Network Recovery-as-a-Service focuses on restoring network services, minimizing downtime, and maintaining public IP addresses during unexpected outages. That matters because customers, staff, vendors, and remote users still need a familiar path into recovered systems.
What Modern Disaster Recovery Needs in 2026
A current disaster recovery plan needs a few layers working together.
1. A Protected Copy That Attackers Can’t Quietly Alter Or Erase
That’s where immutable backups come in. An immutable backup stays locked for a defined retention period. Nobody can modify or delete it during that window, even if they’ve gained high-level access. This is the core value of immutability. It gives the business a copy that stays intact when other paths fail. For example. Stage2Data’s storage model uses S3 storage with object locking to create that write-once, read-many behavior.
That connection matters. Immutability is the outcome. Object locking is the control that enforces it. S3 storage is the storage layer that many teams use to apply that control at scale. If a recovery design claims to protect backups from ransomware, those details matter. Otherwise, the “protected” copy may still be a copy that a compromised admin account can destroy.
2. Isolation
Many teams still think first of air-gapped backups, and those still have a place. Offline or physically separated copies can be very effective when you need one layer that the main network can’t touch. But physical separation can slow down restore operations, especially when large datasets and application dependencies have to come back under pressure.
Many modern environments now blend air-gapped backups with virtual isolation, cloud vaulting, and strict access controls to preserve separation without making recovery painfully slow. Stage2Data’s Cleanroom offers this service: A virtual air gap built through locked backup copies and software-defined isolation.

3. Clean Recovery
Teams need to know that the restore point they’re using won’t simply reintroduce malware or attacker persistence. That means scanning restore points, validating critical services in isolation, and controlling how recovered workloads reconnect to the rest of the environment. We recommend recovering into a clean, network-isolated location and check backup data before restore. Stage2Data’s cleanroom solution follows the same logic by using an isolated recovery environment built around immutable backup copies and software-defined separation.
4. Speed with Structure
Cloud-based disaster recovery and disaster recovery-as-a-service (DRaaS) only help if they shorten the real disruption. Stage2Data’s DRaaS solution replicates and recovers the full IT environment with minimal downtime. That matters because serious incidents rarely leave time for an in-place rebuild before the business needs systems back. Recovery has to start in a controlled, alternate environment that’s already ready to host the workload.
5. A Real Failback Plan
Plenty of teams can talk about failover. Fewer can explain how they’ll return operations to the intended primary environment without confusion, rushed cutovers, or weeks of drag. A full disaster recovery plan has to treat failback as part of the main design, not as a later clean-up step.
Best Practices for a Stronger Disaster Recovery Plan
A stronger disaster recovery plan starts with prioritization. Teams should know:
- Which systems the business can’t operate without.
- Which dependencies those systems rely on.
- How long each one can realistically stay down before the damage becomes unacceptable.
That gives recovery an order. Without it, teams restore what’s loudest, not what matters most. Organizations are encouraged to identify critical data, applications, and business functions before an incident so recovery can follow a defined sequence.
The next step is to review where backup copies sit and who can touch them. At least one protected copy should live outside the same administrative and operational boundary as production, and that copy should use immutable backups with object locking. If a backup environment places too much trust in the main environment, attackers may be able to cross into it using the same credentials or tooling they used in production. Stage2Data’s object-locking model is built around the assumption that intruders may get inside the main network and may even gain privileged access.
Teams should also test for cleanliness, not only recoverability. It isn’t enough to say, “the restore completed.” A useful test asks tougher questions:
- Was the restore point clean?
- Did core services start correctly in isolation?
- Could staff reach them?
- Could the team document each step well enough for legal, insurance, and executive review?
Research links backup verification to faster recoveries and lower reinfection rates, which makes this one of the highest-value habits a team can build.
Network behavior needs a test, too. Recovered services have to be reachable, and reachability often depends on more than compute and storage. It may depend on IP preservation, DNS, routing, authentication, application gateways, and user access patterns. Stage2Data’s service pages and case material both stress this point by focusing on native user connectivity and maintaining public-facing network identity during failover.
Finally, teams should rehearse failback separately from failover. Failback means changed data must move in the right direction, replication must be re-established correctly, and user impact must remain controlled while workloads return home. If that process hasn’t been planned, recovery can feel “done” while the business is still operating in a temporary state that carries cost and risk. Stage2Data’s recent case work shows how important that steady hand is during extended recoveries.
A Real Example of Modern DR Under Pressure
Stage2Data’s recent case study is a useful example because it shows what disaster recovery looks like when the issue goes beyond simple data restore. In that case, a ransomware attack compromised the customer’s primary data center. Stage2Data moved the customer’s environment into its hosting infrastructure to maintain operations while the client rebuilt on new hardware. The recovery stayed active for five months before Stage2Data helped with controlled failback and the re-establishment of replication.
A few details from that case are worth noting. Stage2Data restored additional virtual machines from archived backups when the client identified gaps in the original replication set. It extended the client’s network into the DR environment so workloads could keep their network identities and users could connect normally. At peak, the hosted recovery environment supported over 50TB of systems. That’s a better picture of modern disaster recovery than a simple “we restored from backup” story. It shows hosted operations, archive recovery, network continuity, and phased return to normal operations working as one process.
Another case reinforces the same lesson. We added archival storage to the client’s S3 storage, creating an air-gapped long-term backup with object locking and immutable snapshots that the attackers couldn’t touch. That’s exactly the kind of layered design many organizations now need. Fast replication and failover are important, but they don’t remove the need for a separate protected copy.
The New Standard for Disaster Recovery
The standard has moved. In 2026, disaster recovery must assume attackers may reach production, credentials, backup tooling, and the recovery workflow itself. That’s why a current disaster recovery plan can’t stop at retention schedules and routine restores. It needs immutable backups, object locking, isolation, clean validation, cloud-based disaster recovery, and a disaster recovery-as-a-service model that can support both fast recovery and controlled failback. It all points in the same direction: Recovery now has to be designed as carefully as protection.
For teams reviewing their options, the better question isn’t “Do we have backups?” It’s “Can we recover when attackers target backups too?” Stage2Data’s approach to DRaaS, S3 storage, object locking, cleanroom recovery, and network recovery is built around that exact problem. And that’s the shape modern disaster recovery needs now.
FAQ about Disaster Recovery in 2026
What are the 4 C's of disaster recovery?
In practice, the four areas that matter most are copies, cleanliness, connectivity, and continuity. You need protected backup copies, clean restore points, working network access during failover, and a continuity plan that covers both recovery and failback.
What does ransomware do to the files it gets control of?
Ransomware usually encrypts files so users can’t open them. In many incidents, attackers also steal data, delete connected backups, and interfere with the systems around those files to make recovery harder and put more pressure on the victim.
Can immutable backups be compromised?
Immutable backups are much harder to alter or delete during their retention period, but they don’t remove every risk. Attackers may still compromise production systems, steal credentials, disrupt backup management tools, or corrupt data before it’s backed up. That’s why immutable backups work best as part of a wider disaster recovery plan that includes isolation, access controls, clean recovery checks, and tested restore procedures.
Join the Stage2Data Partner Program
The DRaaS market is growing fast, and MSPs have an incredible opportunity to lead the way. Partnering with Stage2Data means offering your clients more than just disaster recovery. It means giving them better value, service, and peace of mind—all while growing your own business.
Getting started is easy. Our team will guide you through the process, from initial setup to training and beyond. You’ll have access to the tools and support you need to succeed, all without the red tape that comes with larger providers.